Technology
Unmasking Privacy: Four Common Myths and Their Realities

Recent high-profile data breaches have raised serious concerns regarding online privacy, prompting many individuals to question the security of their personal information. Notable incidents affecting companies such as Canada Goose, SoundCloud, and WestJet have exposed millions of accounts, highlighting vulnerabilities that could affect anyone. In light of these events, it is crucial to debunk common misconceptions about online privacy that could inadvertently compromise user data.
Understanding Common Privacy Myths
A prevalent belief among internet users is that strong passwords alone are sufficient for protecting their accounts. However, cyber experts stress the importance of not reusing passwords across different platforms. If one service is compromised, cybercriminals may exploit the same password on other accounts, regardless of its complexity. This notion extends to the assumption that only wealthy or famous individuals are targets for hackers. In reality, everyone’s data holds value, making it essential to take precautions.
To enhance security, individuals are advised to employ unique passwords for each online account. Utilizing reputable password manager applications can simplify this task. Additionally, embracing “passkeys” that utilize biometric features, such as fingerprints or facial recognition, offers an extra layer of protection. Implementing multi-factor authentication (MFA) is also recommended, requiring users to provide a one-time code sent to their mobile devices, significantly reducing the risk of unauthorized access.
The Reality of Private Browsing Modes
Another widespread myth is the belief that using private browsing modes, often labeled as “Incognito” or “In-Private,” guarantees complete privacy. While these modes prevent local storage of browsing history and cookies, they do not shield users from being tracked by Internet Service Providers (ISPs) or the websites visited. According to Iskander Sanchez-Rola, director of AI & Innovation at Norton, online activity remains visible and could potentially be shared or sold to third parties.
For those concerned about privacy, installing a reputable Virtual Private Network (VPN) can help mask IP addresses and encrypt internet traffic. Additionally, employing anti-tracking solutions and maintaining an up-to-date security suite can further protect against unwanted data collection.
Another common misconception is that deleting data from devices completely erases it. Many users believe that emptying the Recycling Bin or formatting storage devices permanently removes files. In reality, cybercriminals can often recover deleted files using accessible recovery tools, making it critical to take proper measures before disposing of old technology.
To securely erase personal data, users can utilize specialized software designed to overwrite files on hard drives or flash drives. Tools like CBL Data Shredder and Eraser can ensure comprehensive data removal. For smartphones and tablets, factory resets usually suffice due to built-in encryption. However, reputable organizations, such as Canada’s Electronic Products Recycling Association (EPRA), offer services that guarantee complete data destruction on donated devices.
Social Media Privacy: The Hidden Risks
Finally, many people mistakenly believe that setting their social media profiles to “Private” ensures that only friends can view their information. While Facebook provides the option to control visibility, private profiles can still expose personal details, such as names, profile pictures, and user IDs. Users should be mindful of the permissions granted to third-party applications, which may access personal data, including friends lists.
To enhance privacy on social media platforms, users should regularly review their privacy settings and understand what data is being shared. Uninstalling unnecessary third-party apps can help minimize risks associated with data sharing. It is also important to recognize that even seemingly private information can be inadvertently shared through friends’ contact lists or social media interactions.
In conclusion, as the digital landscape continues to evolve, understanding the limitations of online privacy is vital. By debunking these common myths and implementing robust security measures, internet users can better protect their personal information in an increasingly interconnected world.
-
 Education7 months ago
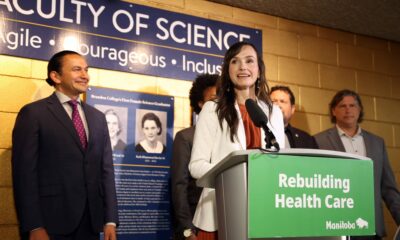
Education7 months agoBrandon University’s Failed $5 Million Project Sparks Oversight Review
-
 Science8 months ago
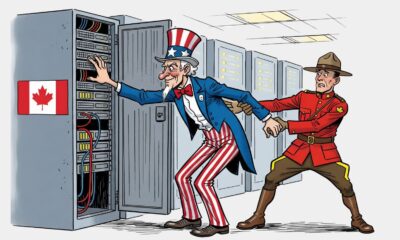
Science8 months agoMicrosoft Confirms U.S. Law Overrules Canadian Data Sovereignty
-

 Lifestyle7 months ago
Lifestyle7 months agoWinnipeg Celebrates Culinary Creativity During Le Burger Week 2025
-

 Lifestyle4 months ago
Lifestyle4 months agoDiscover Aritzia’s Latest Fashion Trends: A Comprehensive Review
-

 Education8 months ago
Education8 months agoNew SĆIȺNEW̱ SṮEȽIṮḴEȽ Elementary Opens in Langford for 2025/2026 Year
-

 Business4 months ago
Business4 months agoEngineAI Unveils T800 Humanoid Robot, Setting New Industry Standards
-

 Health8 months ago
Health8 months agoMontreal’s Groupe Marcelle Leads Canadian Cosmetic Industry Growth
-

 Science8 months ago
Science8 months agoTech Innovator Amandipp Singh Transforms Hiring for Disabled
-

 Technology8 months ago
Technology8 months agoDragon Ball: Sparking! Zero Launching on Switch and Switch 2 This November
-
 Technology3 months ago
Technology3 months agoDigg Relaunches as Founders Kevin Rose and Alexis Ohanian Join Forces
-

 Lifestyle4 weeks ago
Lifestyle4 weeks agoCanmore’s Le Fournil Bakery to Close After 14 Successful Years
-

 Top Stories4 months ago
Top Stories4 months agoCanadiens Eye Elias Pettersson: What It Would Cost to Acquire Him
-

 Health7 months ago
Health7 months agoEganville Leader to Close in 2026 After 123 Years of Reporting
-

 Education8 months ago
Education8 months agoRed River College Launches New Programs to Address Industry Needs
-

 Top Stories4 months ago
Top Stories4 months agoNicol Brothers Shine as Wheat Kings Dominate U18 AAA Hockey
-

 Business8 months ago
Business8 months agoBNA Brewing to Open New Bowling Alley in Downtown Penticton
-

 Business7 months ago
Business7 months agoRocket Lab Reports Strong Q2 2025 Revenue Growth and Future Plans
-

 Education6 months ago
Education6 months agoAlberta Petition Aims to Redirect Funds from Private to Public Schools
-

 Lifestyle5 months ago
Lifestyle5 months agoEdmonton’s Beloved Evolution Wonderlounge Closes, New Era Begins
-

 Education8 months ago
Education8 months agoAlberta Teachers’ Strike: Potential Impacts on Students and Families
-

 Technology6 months ago
Technology6 months agoDiscord Faces Serious Security Breach Affecting Millions
-

 Technology8 months ago
Technology8 months agoGoogle Pixel 10 Pro Fold Specs Unveiled Ahead of Launch
-

 Business7 months ago
Business7 months agoIconic Golden Lion Restaurant in South Surrey to Close After 50 Years
-
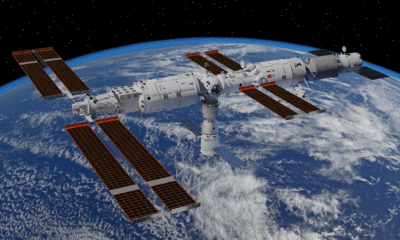
 Science8 months ago
Science8 months agoChina’s Wukong Spacesuit Sets New Standard for AI in Space










