Science
Cybercriminals Recruit Insiders via Dark Web for Corporate Breaches

Cybercriminals are increasingly using the dark web to recruit insiders from various organizations, posing a significant threat to corporate security. These activities include both public recruitment posts and private messages on professional networking platforms like LinkedIn. By enlisting malicious insiders, cybercriminals can gain direct access to sensitive company resources, enabling them to steal confidential data or execute devastating cyberattacks.
Research conducted by cybersecurity firm NordStellar has identified dark web posts from users actively seeking employees from specific organizations over the past year. A notable focus of these posts is on insiders working for social media and cryptocurrency platforms. For example, in 2025, the cryptocurrency exchange platform Coinbase revealed that it had fallen victim to a breach where cybercriminals bribed employees to leak user information.
According to Vakaris Noreika, a cybersecurity expert at NordStellar, the methods of recruitment vary significantly. While some cybercriminals openly advertise the need for insiders through dark web posts, others adopt a more discreet approach. Over the past 12 months, NordStellar’s team identified 25 unique posts that specifically targeted employees within certain organizations.
Understanding Insider Threats
Insider threats take on a new dimension as they provide cybercriminals with access to critical data, including personal customer information and confidential business agreements. Noreika explains, “This data can be utilized to deploy ransomware attacks, sell intelligence on business agreements to competitors, or carry out sophisticated phishing scams on unsuspecting victims whose personal data they managed to obtain.”
The challenge with insider threats lies in their often undetectable nature. Employees, being trusted members of the organization, have legitimate access to company resources, making it difficult to identify any anomalies in their behavior. Noreika notes that unlike external threats, insiders may not trigger typical security alerts, such as unusual login attempts or data transfers. They are also familiar with the organization’s internal security policies, allowing them to adjust their actions to avoid suspicion.
Combatting Insider Recruitment
While cybercriminals are increasingly seeking insiders through the dark web, Noreika emphasizes that recruitment processes are usually carried out privately. These bad actors target specific employees, particularly those with technical expertise or access to highly sensitive data.
To safeguard against insider threats, businesses must establish a strong cybersecurity strategy that emphasizes high observability into system and data usage. Noreika advises that any unexpected system behavior or access patterns should be flagged, reported, and thoroughly examined. “Patterns of unusual behavior are the first indicator that a user might be an insider,” he says. Security teams should monitor employees who frequently access sensitive information to ensure they possess the proper authorization. Data exfiltration to external parties or devices is another major red flag.
Furthermore, having an incident recovery plan is crucial for minimizing the fallout from a cyberattack originating from insider threats. This plan should cover incident detection and outline key steps the organization should take to contain the threat and mitigate damage.
In related news, Google has announced its intention to shut down its dark web monitoring tool, the Dark Web Report, which was designed to scan the dark web for exposed personal information. The shutdown is scheduled for January 15, 2026, with scans for new dark web breaches ceasing on that date. The Dark Web Report will no longer be available after February 16, 2026, and all data related to the report will be deleted. Google has indicated a desire to focus on tools that provide clearer, actionable steps for customers to protect their online information, though no specific announcements regarding new cybersecurity tools have been made.
As cybercriminals continue to adapt their tactics, the need for robust cybersecurity measures that address both external and internal threats has never been more critical. Organizations must remain vigilant in monitoring employee behavior and protecting sensitive data to thwart the growing risks posed by insider recruitment on the dark web.
-
 Education7 months ago
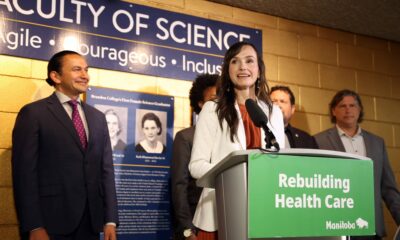
Education7 months agoBrandon University’s Failed $5 Million Project Sparks Oversight Review
-
 Science8 months ago
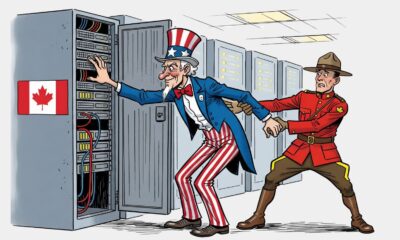
Science8 months agoMicrosoft Confirms U.S. Law Overrules Canadian Data Sovereignty
-

 Lifestyle7 months ago
Lifestyle7 months agoWinnipeg Celebrates Culinary Creativity During Le Burger Week 2025
-

 Lifestyle4 months ago
Lifestyle4 months agoDiscover Aritzia’s Latest Fashion Trends: A Comprehensive Review
-

 Education8 months ago
Education8 months agoNew SĆIȺNEW̱ SṮEȽIṮḴEȽ Elementary Opens in Langford for 2025/2026 Year
-

 Business4 months ago
Business4 months agoEngineAI Unveils T800 Humanoid Robot, Setting New Industry Standards
-

 Health8 months ago
Health8 months agoMontreal’s Groupe Marcelle Leads Canadian Cosmetic Industry Growth
-

 Science8 months ago
Science8 months agoTech Innovator Amandipp Singh Transforms Hiring for Disabled
-

 Technology8 months ago
Technology8 months agoDragon Ball: Sparking! Zero Launching on Switch and Switch 2 This November
-
 Technology3 months ago
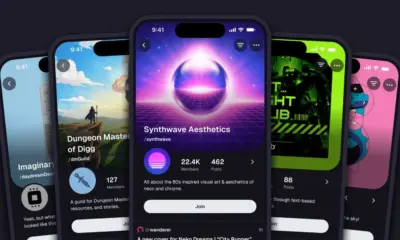
Technology3 months agoDigg Relaunches as Founders Kevin Rose and Alexis Ohanian Join Forces
-

 Lifestyle4 weeks ago
Lifestyle4 weeks agoCanmore’s Le Fournil Bakery to Close After 14 Successful Years
-

 Top Stories4 months ago
Top Stories4 months agoCanadiens Eye Elias Pettersson: What It Would Cost to Acquire Him
-

 Health7 months ago
Health7 months agoEganville Leader to Close in 2026 After 123 Years of Reporting
-

 Education8 months ago
Education8 months agoRed River College Launches New Programs to Address Industry Needs
-

 Business8 months ago
Business8 months agoBNA Brewing to Open New Bowling Alley in Downtown Penticton
-

 Top Stories4 months ago
Top Stories4 months agoNicol Brothers Shine as Wheat Kings Dominate U18 AAA Hockey
-

 Business7 months ago
Business7 months agoRocket Lab Reports Strong Q2 2025 Revenue Growth and Future Plans
-

 Education6 months ago
Education6 months agoAlberta Petition Aims to Redirect Funds from Private to Public Schools
-

 Lifestyle5 months ago
Lifestyle5 months agoEdmonton’s Beloved Evolution Wonderlounge Closes, New Era Begins
-

 Education8 months ago
Education8 months agoAlberta Teachers’ Strike: Potential Impacts on Students and Families
-

 Technology6 months ago
Technology6 months agoDiscord Faces Serious Security Breach Affecting Millions
-

 Technology8 months ago
Technology8 months agoGoogle Pixel 10 Pro Fold Specs Unveiled Ahead of Launch
-

 Business8 months ago
Business8 months agoIconic Golden Lion Restaurant in South Surrey to Close After 50 Years
-

 Lifestyle6 months ago
Lifestyle6 months agoCanadian Author Secures Funding to Write Book Without Financial Strain










